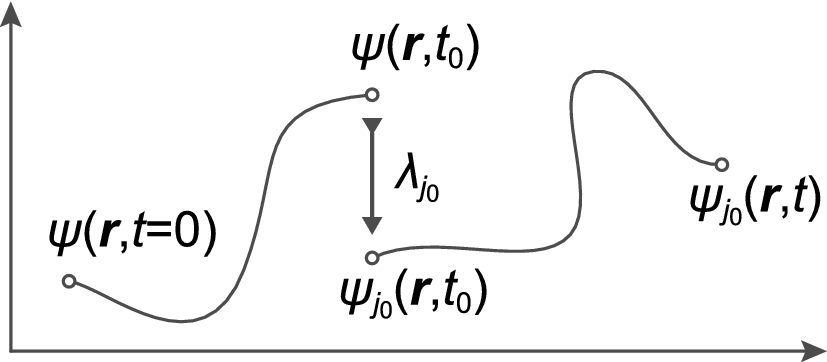
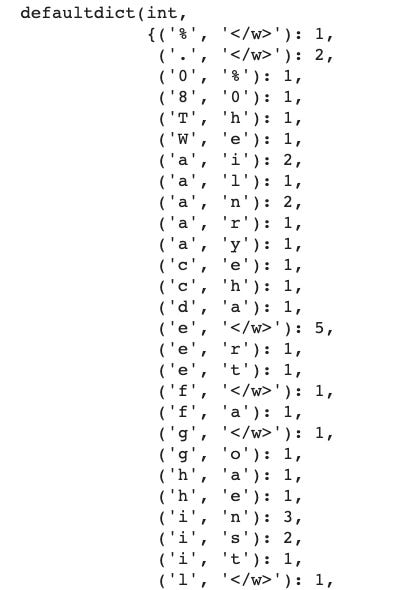
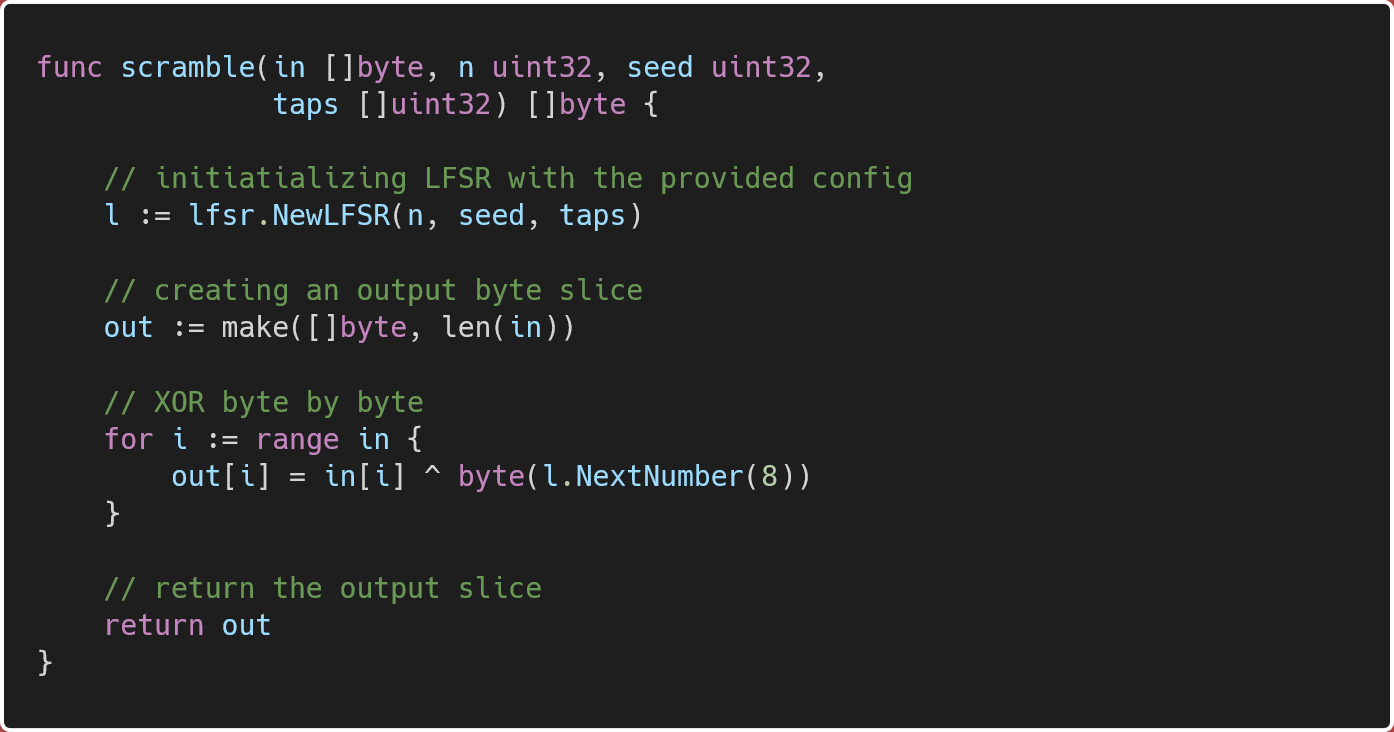
Electronics | Free Full-Text | Magniber v2 Ransomware Decryption: Exploiting the Vulnerability of a Self-Developed Pseudo Random Number Generator | HTML

BBS-BitsBytes & STEM Online Tutorial Video Program - For O and A Level Extra Classes - BBS-BitsBytes & STEM
Proof of knowledge revealed message structure · Issue #10 · decentralized-identity/bbs-signature · GitHub
GitHub - jaygooby/ttfb.sh: Measures time-to-first-byte in seconds, for single or multiple URLs. Can calculate fastest, slowest & median TTFB values, and optionally log all response headers. Uses curl and the calculation `%{time_starttransfer} - %{



![How to generate Random numbers using the nextBytes(byte[] bytes) method of Random Class? - YouTube How to generate Random numbers using the nextBytes(byte[] bytes) method of Random Class? - YouTube](https://i.ytimg.com/vi/egHVpqxNgS0/mqdefault.jpg)