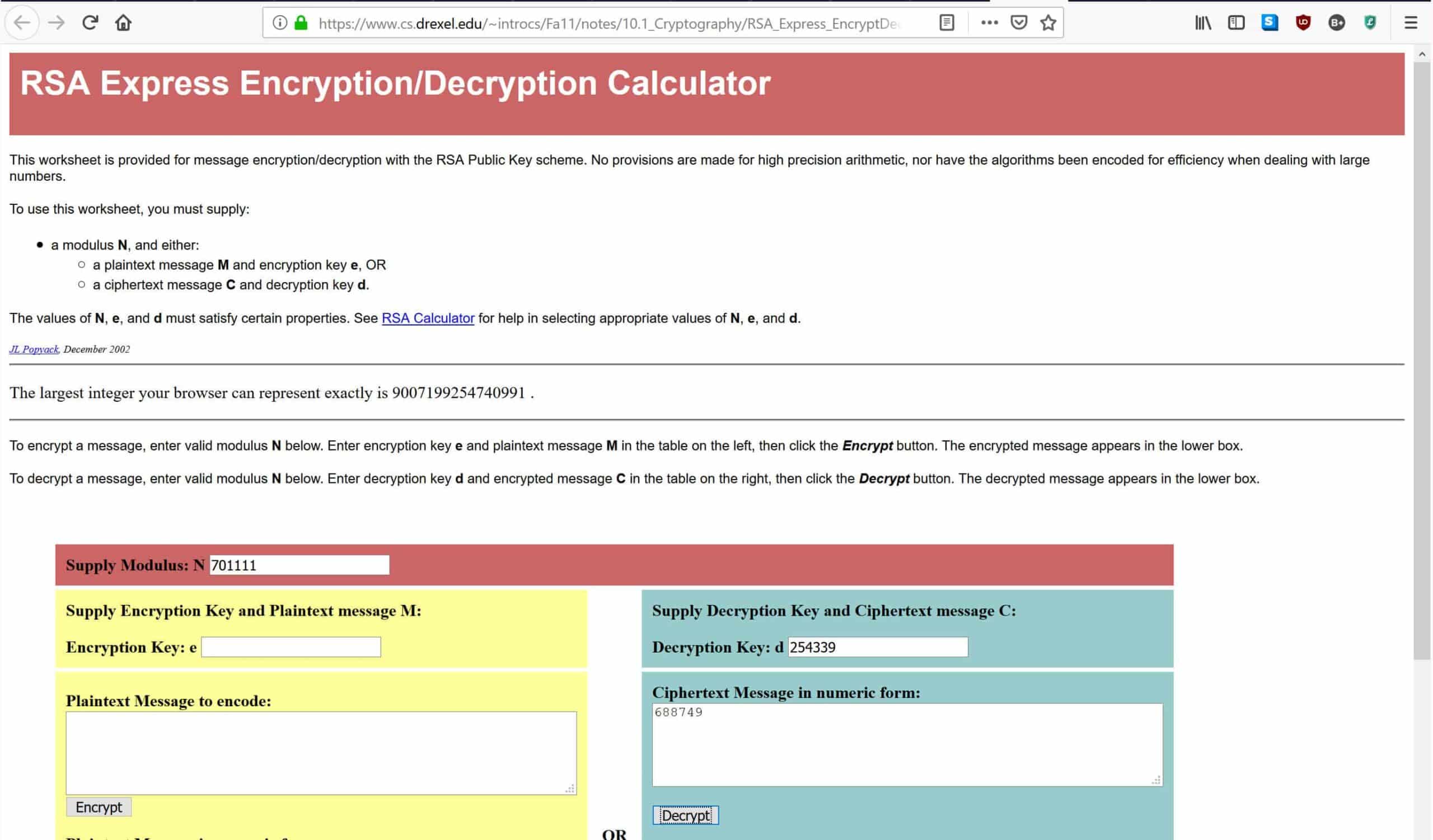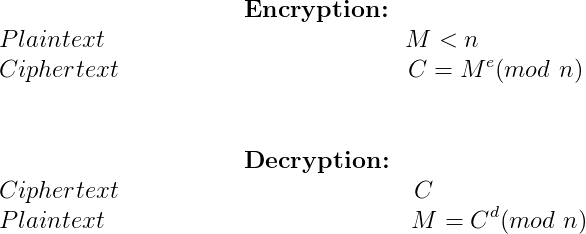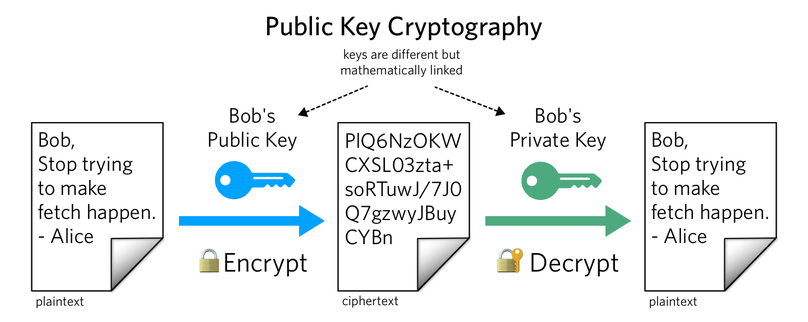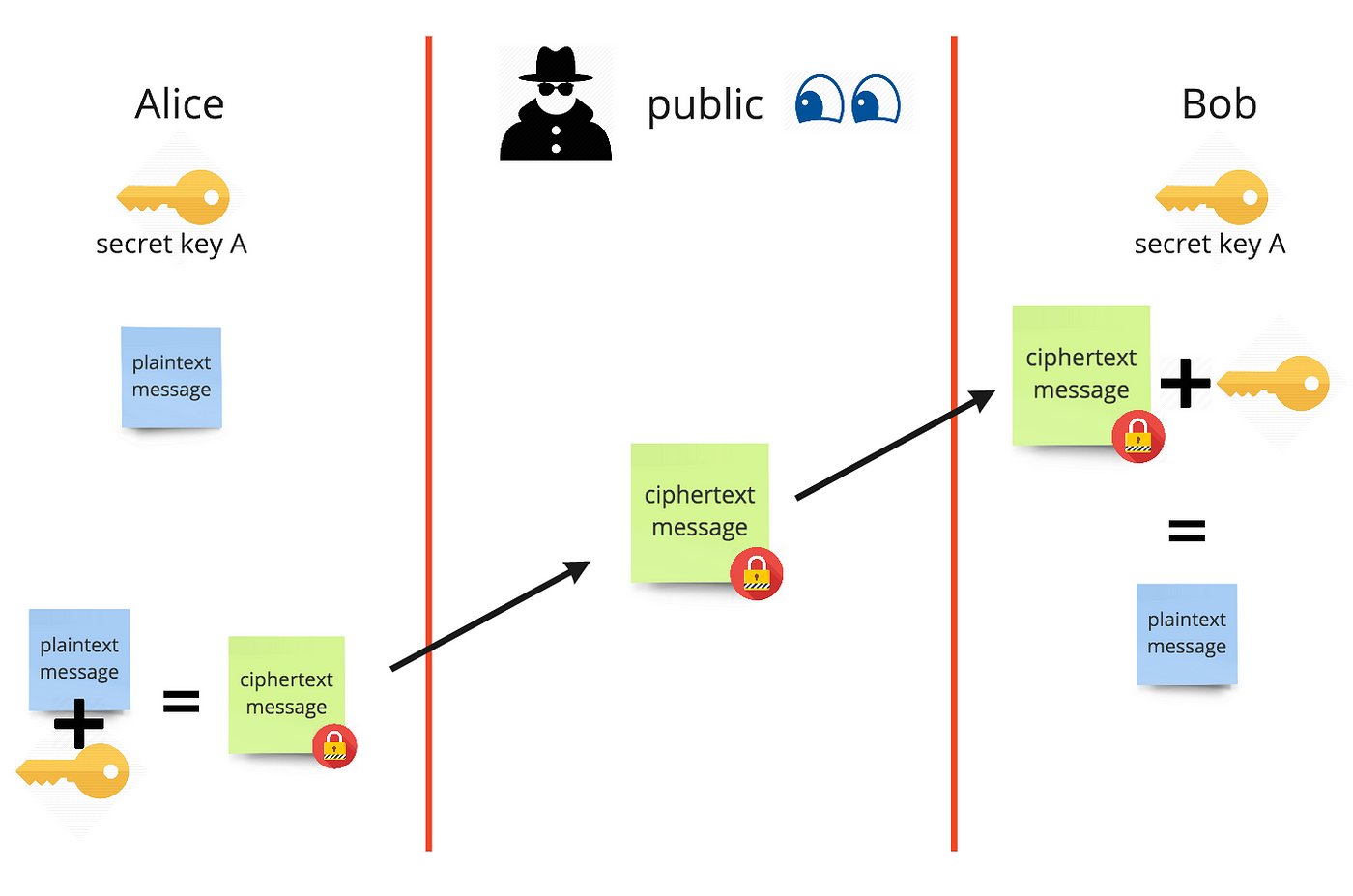
Electronics | Free Full-Text | New RSA Encryption Mechanism Using One-Time Encryption Keys and Unpredictable Bio-Signal for Wireless Communication Devices | HTML
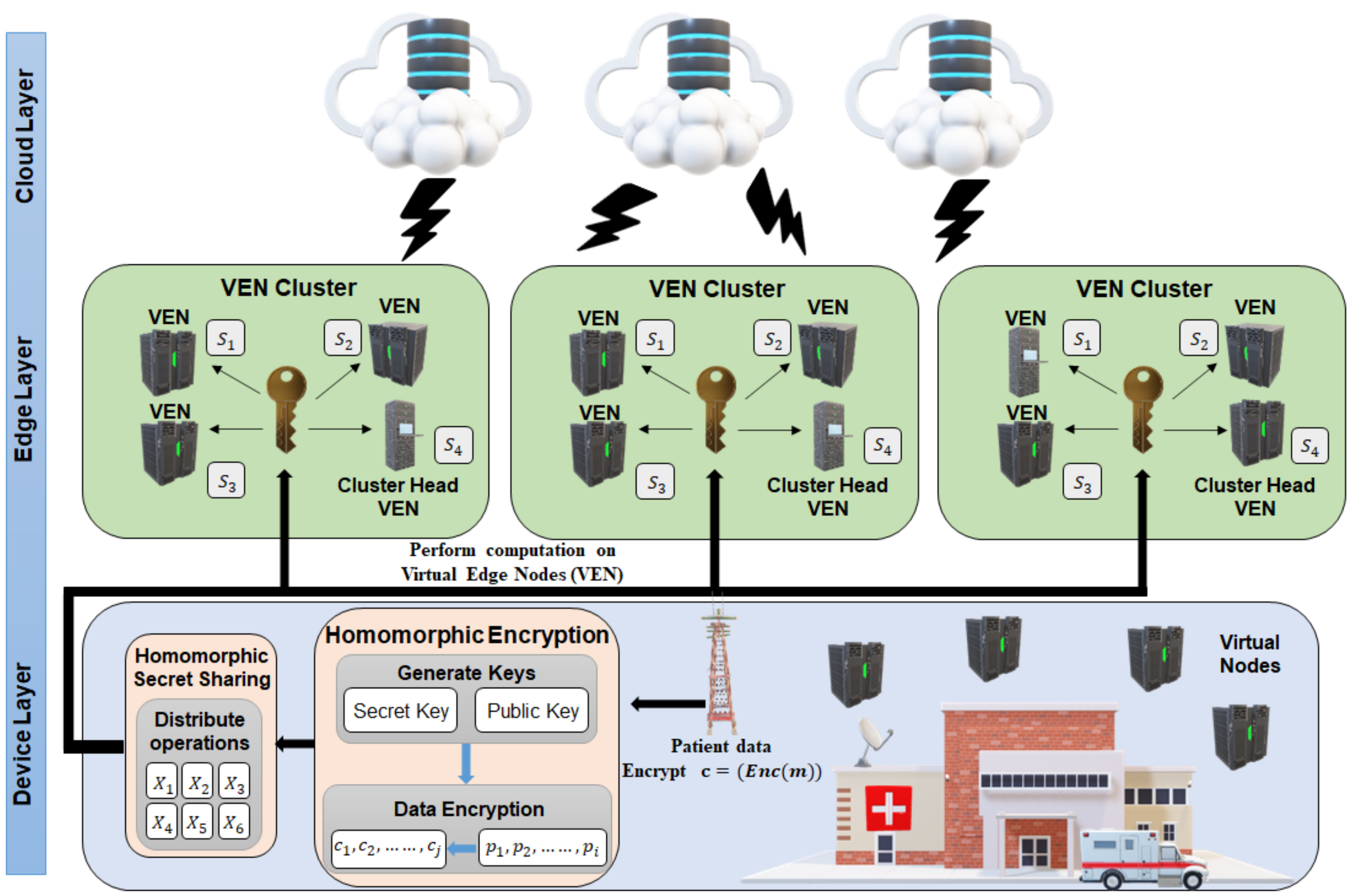
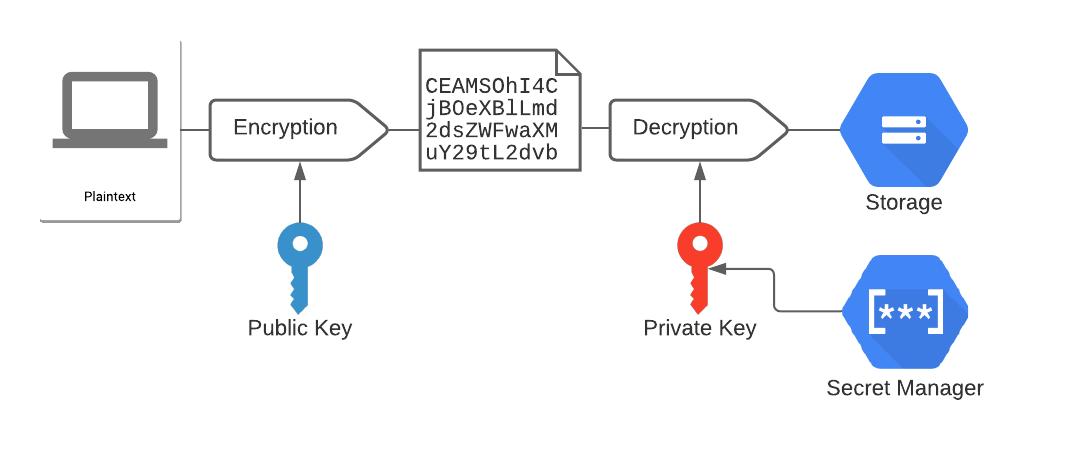
Applied Sciences | Free Full-Text | Homomorphic Encryption Based Privacy-Preservation for IoMT | HTML
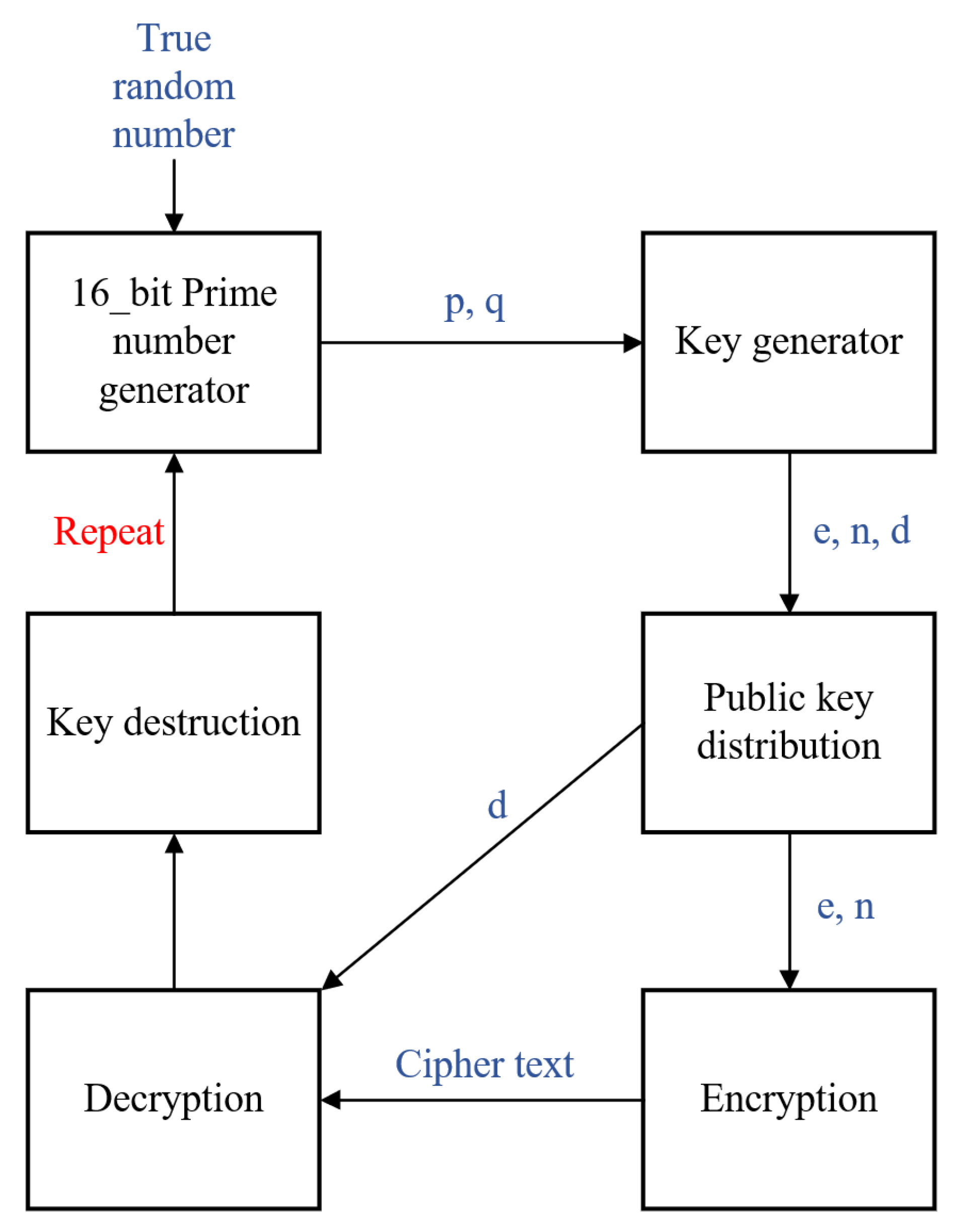
Link Key generation Encryption keys: The encryption key is generated... | Download Scientific Diagram